Blog roll please!
Quick reads across a variety of topics
Diode: The First Open-Source Blockchain-Based Alternative to Ngrok
Diode
14 Jul
01:30
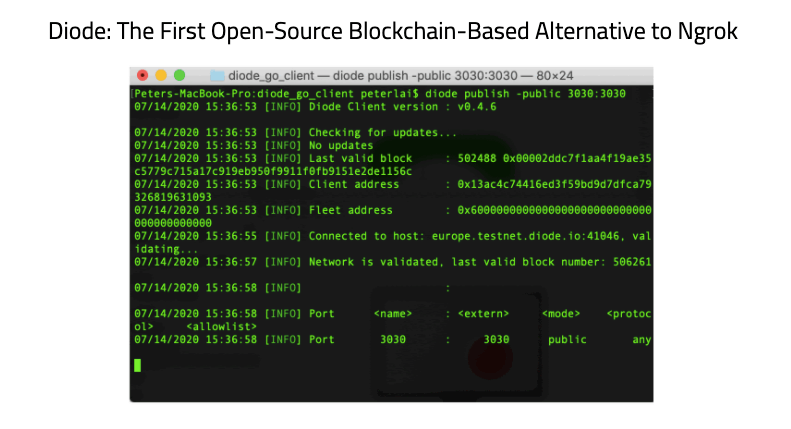
Diode is an open-source blockchain-based peer-to-peer network that enables developers to create applications for various decentralized projects. One of the popular applications that is being developed recently is using Diode as a blockchain implementation of Ngrok. To use Diode, the first open-source, blockchain-based Ngrok alternative, written in Go, install the Diode Client using the curl command: $ curl -Ssf https://diode.io/install.sh | bash Go to Download. Open a terminal window and run the curl command so...
Diode Network and Video Streaming Using Raspberry Pi Zero W
Diode
07 Jul
00:30
Diode’s second livestream meetup event went live on Tuesday (June 30). The 30-minute online event drew some 20 engineers, developers, makers, Raspberry Pi enthusiasts from countries across the globe. CTO Dominic Letz and blockchain engineer Peter Lai were the featured speakers. The meetup topic was about how to perform video streaming using Raspberry Pi Zero W via Diode network. Check out the Diode meetup presentation slides on GitHub. Watch the livestream-ed meetup on YouTube. Peter...
June 2020 Update
Diode
16 Jun
09:10

Since our last development update in February we’re now just getting over the extended periods of Covid forced home-office. While our Taiwan office was only little affected by Covid19 and has had business as usual since quite a time. In our German office we’re just returning now to a somewhat normal. Hope you guys are all well - keep safe. That said, let’s have a look at the development we got done in those last...
Diode CTO Dominic Letz Featured on the Weekly DeFi Podcast
Diode
13 Jun
14:31

Our CTO Dominic Letz was invited to go on the Weekly DeFi podcast as a guest recently. Dominic and the Boston-based podcast host Thomas, did the interview over the Internet, talked about the future of the Internet, what is the Web3 revolution, how time is a fundamental problem with Internet security, what is the Diode Network, and more importantly, how you can make a positive impact in the Web3 ecosystem. Have a listen here. A...
How to Publish Your Local Web Server to Web3 with Diode
Diode
23 May
19:01
On Tuesday (May 19), Diode’s highly anticipated live streaming event went live. The 30-minute online meetup event drew more than 35 engineers, developers, makers, and community leaders across the globe. CEO Hans Rempel, CTO Dominic Letz, blockchain engineer Peter Lai, marketing manager Yahsin Huang gathered together remotely to discuss some current and potential applications of the Diode’s peer-to-peer network. We gave a demo of Diode client showcasing how to easily publish a local webserver to...
Diode FAQ
Diode
23 May
16:00
This page was moved Please click here for the most recent FAQ Below is the old version of the FAQ General Questions What is Diode? Diode is an integrated Blockchain implementation of the Web3, the server-less internet and the decentralized web, targeted primarily at enabling IoT devices. It was designed to address the security and infrastructure needs of device-driven connected applications. Where did the name “Diode” come from? We went back and forth with a...
Diode Meetup Event Recap
Diode
06 May
00:10

Diode’s first livestream event went live on Monday, April 27, in Taipei, Taiwan. The 2.5-hour online meetup drew more than 30 engineers, developers, makers, and community leaders. Below are some highlights from the event, which was moderated by Raspberry Pi Taiwan group leader Hsu, the featured speaker was Dominic Letz, CTO of Diode. Watch Dominic’s talk on YouTube. Diode’s presentations slides are now publicly available on Github. At the event, Dominic talked about a desired...
EthCC Paris Recap
Diode
30 Mar
23:36

This month, the Diode team spent a week in Paris for EthCC 3 event. Here is a recap of some of the most interesting things we have seen. Hundreds of developers, researchers, investors, and aspiring founders gathered in Paris earlier this month for the third annual Ethereum Community Conference (EthCC). Held in the 5th arrondissement of Paris on March 3-5, CTO Dominic Letz and team members were able to connect globally at the forefront of...
New Edge Protocol In The Testnet
Development
23 Mar
11:29
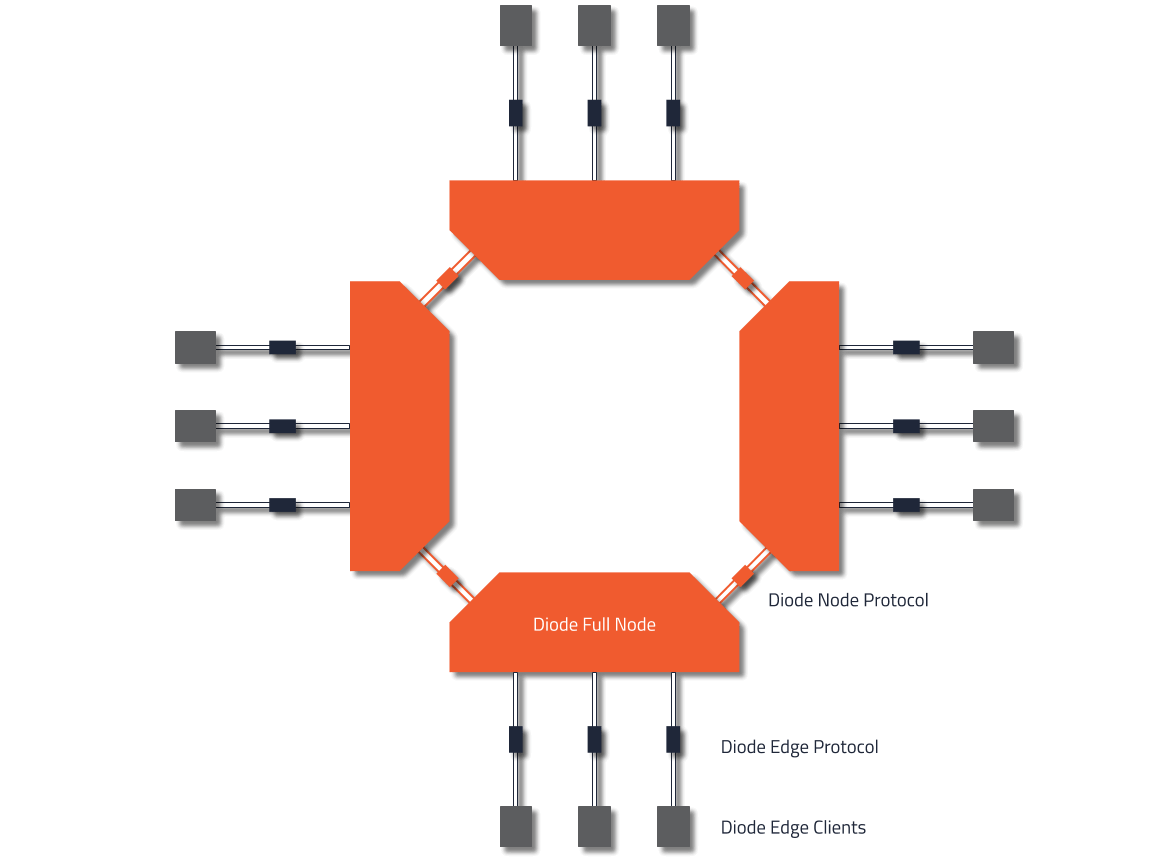
With the next major client update the Diode network will be using a new Edge Network Protocol. Edge2 is replacing the current Edge1 protocol. Nodes will be supporting both protocols for some time until all clients are being upgraded. The new protocol brings major enhancements. First and foremost the protocol change enables full async messaging and will remove those pesky timeout issues. In addition the change from JSON to RLP for protocol encoding is halving...
The Stanford Blockchain Conference 2020 Recap
Diode
20 Mar
00:24

The 4th Stanford Blockchain Conference (SBC) continues to educate attendees about the research and current issues around blockchain protocol development, cryptography, distributed systems, and crypto-economics. The 3-day event was held from February 19 to 21 at Arrillaga Alumni Center, Stanford University in California. Hosted by The Stanford Center for Blockchain Research, the event was free of charge and open to the public. Our team members blockchain engineer Peter and marketing Yahsin traveled from Taiwan to...
